If SI has said it once, SI has said it a million times.
There’s no better or safer mobile platform than iOS, Apple’s tightly controlled operating system for iPhones and the iPad tablets.
A new study has come out on mobile platform security and if you’re an Android user I’d strongly recommend you start rolling your weed to calm your nerves before reading any further.
Android – No-1 Malware Target
In 2012, Android continued to be the favorite choice of the whackos, crackheads and the Dr.Hannibal Lecters.
According to the NQ Mobile’s 2012 Security Report, 94.8% of malware discovered in 2012 was designed to attack Android devices compared to a mere 4% that targeted Symbian.
The NQ Mobile folks estimate infected Android devices rose in excess of 200% in 2012 – Over 32.8 million Android devices were infected in 2012 compared to 10.8 million in 2011.
There are three reasons why Android continues to be the favorite haunt of the nut jobs and the Hannibal Lecters.
First, a lot of Android users continue to run older versions of the software – More than 39% of Android users are still using Gingerbread, which lacks the major security updates of Ice Cream Sandwich and Jelly Bean.
Second, sideloading of apps from third party marketplaces (the process of download and installing mobile apps outside of Google Play) is exacerbating the malware epidemic among Android users. Apparently, the majority of malicious apps are hosted at third party Android marketplaces.
The younger generation of smartphone users, i.e. those in the 13-17 age group, are more likely to download apps outside of the relatively safe haven of Google Play.
India Hit Badly
India is one of the biggest victims of the mobile malware explosion.
NQ Mobile estimates that 19.4% of infected devices were in India.
Mera Bharat Mahaan was second only to China in number of infected devices.
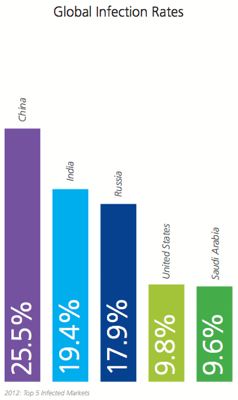
Given my suspicion that a lot of malicious online attacks originate in China, it’s no surprise that the highest number of infected devices (25.5%) are in that nation.
You may consider it the Basmasura Effect or the Law of Unintended Consequences.
How Devices get Infected
App repackaging, malicious URLs and smishing are the three major ways mobile devices pick up malware.
In app repackaging, which is how most infections happen, criminals add lines of malicious code into a genuine app and repackage and reload it onto a third party marketplace for victims to download and install. Once the unsuspecting victim has installed the app, it works in the background to collect user data, change user settings, or remotely control the device to send SMS messages.
Smishing a.k.a. “Toll Fraud” is lucrative to criminals, generating up to $4 USD per SMS. Combining social engineering (phishing) and SMS, smishing tricks consumers into clicking on a malicious link.
Malicious URLs redirect a user from a genuine web site to a clone where the victim’s personal information is stolen. Oftentimes, this involves misuse of stolen information for withdrawing money from banks and other financial institutions.
Other Concerns
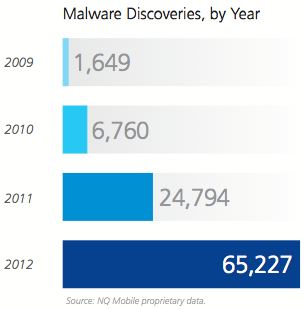
* Mobile malware increased 163% in 2012 to 65,227
* 65% of malware discovered in 2012 falls into the broader category of Potentially Unwanted Programs (root exploits, spyware, pervasive adware and Trojans)
* 7% of malware was designed to “brick” a user’s device, i.e. make it stop working
* VDLoader, a malware affecting Android devices, can hide within genuine apps and has the ability to upgrade itself
Thank You, I’ll stick to my trusted companion iPhone 4.

This is truly horrible.
So what can Android users do to avoid Malware?
Just not download any app?
SearchIndia.com Responds:
You write: So what can Android users do to avoid Malware?
They can chuck their Android phones off the GWB or Queensboro Bridge and get this thing called iPhone…it’s never given SI any malware in 5 years despite visits to naughty sites! 😉
I think ur knowledge on mobile/tech is rather limited as I have observed from ur recent tech related articles.
Do you really think that this statistical data based on some rubbish survey would help u anything from choosing a between an iphone and an android device…. I myself am using Android device since 2 years and I haven’t faced any malware infection even my friends never complained about malware…. Even I visit naughty websites all the time with no issues… All am saying is to try an android device (preferably an htc) for yourself…
Malware is just not the reason to avoid a good android device given its unparalleled level of customization, freedom and s#&t load of features that u can only find in ios 10 when it comes.
SearchIndia.com Responds:
You write: Malware is just not the reason to avoid a good android device given its unparalleled level of customization, freedom
Kid, an Android device may have better features than an iPhone but that’s not the point.
The point is the greater risk of malware that android device owners face!
I personally prefer the vertical integrated model where Apple controls the hardware, software, updates and apps rather than the fragmented Android model where carriers exercise significant sway over the interface and updates leaving you vulnerable.
A lot of Android device users are still running older versions of the software making them susceptible.
Instead of throwing mud on the survey and the messenger, you might want to ponder over the demerits of the horizontal model (Android) vs vertical model (Apple iOS)
I agree with that thing where hardware n software built by the same manufacturer give better results.
But that’s not entirely true because u know how the apple built maps turned out to be, a disaster.
Try a more popular android device manufacturer like Samsung or htc to receive the most recent software updates because only the popular manufacturers are likely to update their devices frequently.
All that being said I’m a great fan of ur movie reviews.
SearchIndia.com Responds:
You are right and wrong on Apple Maps.
You are right that Apple Maps turned out to be significantly inferior to Google Maps.
But you’re wrong in using the Apple maps as an example because Maps is more of a feature than a core piece of the operating system software. You can still go to the Apple AppStore and get the Google Maps.
Using the inferior Apple Maps is an inconvenience but it won’t give you malware but using older versions of Android could make the device more vulnerable.
However, updating the core Android software and getting the latest version is not easily done by all Android device owners even if they happen to own Samsung or HTC devices.
In the U.S., a lot depends on the carrier support for the Android version. For instance, AT&T (a big carrier here) is still selling Samsumg Galaxy and HTC smartphones (Samsung Galaxy Exhilarate and HTC One X) based on the 18-month-old Ice cream Sandwich OS. I am not 100% sure but in the U.S. and a few other countries I don’t think you can update your Android software to the latest version if your carrier does not support them.
Be it the Mac, iPad, iPhone or iPod, Apple has succeeded because of the ease of use and minimal risk to users. That’s the reason iPhone is still the single largest smartphone brand (Android is greater than iOS only when you combine all the Android brand smartphones).
Bottom line, the horizontal model worked well for the PC industry (and Bill Gates’ fortunes) from 1985-2010 but the vertical model of integration is better suited for the mobile world of smartphones, tablets etc.
Your right. Carrier specific devices receive updates slowly especially in US.
But international versions r quick to receive updates. But anyways since u live in US iphone is the best choice.
But I still believe android have some advantages functionally, most important being iTunes independence. You can just drag n drop.
There are some grammatical mistakes in my previous comment as I have found out after posting it .Sorry about that. Try to polish it. Thank you.
Come on SI, you can’t post a shockingly shallow article based on mere numbers. Where is your usual in-depth view?
Thank You, I’ll stick to my trusted companion iPhone 4.
Seriously?
While I am not a fanboy of android nor I hate or loath iPhone, it isn’t fair to compare the working model (not functional/feature set) of iOS and Android. iOS is like a chaste – single-handedly guarded by Apple. Whereas Android is like Throupathai a.k.a open-source platform. It was mainly created for high-level customization which lacked in iOS. Further Google designed only the operating system and let the mobile manufacturers design their own software interface (HTC Sense, Touchwiz, etc). Not all manufacturers were able to exploit all the underlying features of the android which lead to Nexus line which is basically ‘pure’ android with no interface on top.
Not all manufacturers abide to the security guidelines structured by Google. Practically its impossible for Google to check how the companies like Micromax and Karbonn (popular in India for their low-priced smartphones) layout Android on their INR 3000 handset.
Its common sense that the users should download applications only from Google Play where the app undergoes all security checks. Google can keep its premises clean (Google Play) but cannot vouch if the user knowingly download application from third-party website (one reason for this behavior could be many cheap manufacturers don’t provide direct access to Google Play from their devices!).
Bottomline – If you own a popular brand android mobile (Samsung/HTC/Sony) and stick to Google Play for your applications (which has more than what you need), its next to impossible for your mobile to get affected with malwares!
SearchIndia.com Responds:
1. You write: Tt’s common sense that the users should download applications only from Google Play where the app undergoes all security checks…. If you own a popular brand android mobile (Samsung/HTC/Sony) and stick to Google Play for your applications …..its next to impossible for your mobile to get affected with malwares!
Really?
Sweetie, you’re probably too busy to keep up with developments in the digital media arena. The last couple of days has only brought more bad news for Android users, particularly for millions of device owners who downloaded apps from the Google Play store that you so strongly recommend!
Please see:
http://www.zdnet.com/android-malware-scores-nine-million-downloads-with-fake-ad-network-sdk-7000014326/
http://techcrunch.com/2013/04/20/newly-discovered-android-malware-was-downloaded-millions-of-times/
There’s no denying the iOS ecosystem is more secure than the Android ecosystem. At least, so far!
2. You write: Whereas Android is like Throupathai a.k.a open-source platform. It was mainly created for high-level customization which lacked in iOS.
Open source is one of the great inventions of the 20th century. It gave us Linux, Apache web server etc.
But the average consumer does not give a flying f*ck for open source or closed environment.
All she/he wants is a secure mobile device….and that’s where the Android ecosystem has been found wanting so far.
3. But it’s not all milk and honey for iOS (iPhone/iPad) or OS X (iMac/MacBook) users.
For instance, one of the reasons I’ve not upgraded from iOS 5.x to 6.x on both iPhone and iPad is the serious battery degradation issue.
Apple has been callously indifferent to its customers. And I’m glad Apple is under severe pressure now – http://www.searchindia.com/2013/04/22/apple-unbearable-agony-ahead/
Similarly, there are WiFi issues and screen damage issues with iMac. If Apple users don’t purchase AppleCare (extra 2-years of warranty), they’re screwed because repair costs can easily hit close to $600 for a screen replacement on an iMac!